Problem Symtomps
The operation could not be performed because the OLE DB provider ‘SQLOLEDB’ was unable to begin a distributed transaction. OLE/DB provider returned message: New transaction cannot enlist in the specified transaction coordinator.
Cause
The problem occurs because Microsoft Distributed Transaction Coordinator (MS DTC) is not configured for network access. By default, the network access settings of MS DTC are disabled on new installations of SQL Server 2000 on computers that are running Windows Server 2003.
Resolution
Step 1: Open Component Services Wizard using below steps
Go to -> Start -> All Programs -> Administrative Tools -> Component Services
Step 2: Expand the Componenet Service and Double Click on Computers
Step 3: Right Click on MyCompute and select properties
Step 4: Click on MSDTC Tab and then click on Security Configuration
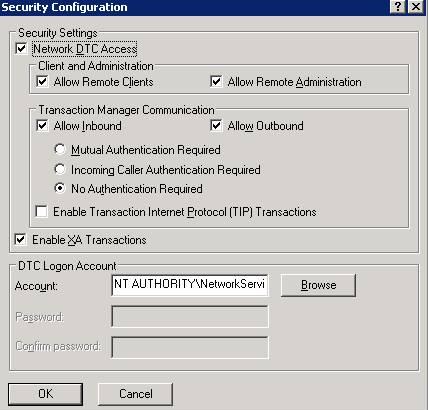
Step 5: In the Security Configuration dialog box, check the Network DTC Access check box
Step 6: Under Network DTC Access, click on New transaction
Please find the below images for the same.

Figure 2

Figure 3